Rethinking Digital Security in the Modern Business Arena
In today’s fast-paced world, where digital transactions and online interactions have become second nature, the importance of security measures on business websites can hardly be overstated. Every time you visit a site like railtech.com, you might be met with a brief and seemingly trivial interruption—a prompt confirming you are human, a verification step designed to guarantee safety against automated bots. But behind this simple screen lies a deep network of safeguards that touches everything from industrial manufacturing to small business operations, and even automotive and electric vehicle innovations.
In this editorial, we will take a closer look at how digital security measures, such as those provided by Cloudflare, add layers of protection and reassurance throughout the digital landscape. We will also explore the additional twists and turns that modern businesses face when dealing with business tax laws, economic news, and marketing strategies. By reflecting on the role of these security challenges and solutions, we can figure a path through what may seem like confusing bits and tricky parts of today’s digital world.
Verification Processes: The First Step in Building Trust
Every time you interact with a website, whether for industrial manufacturing tools or booking a service for an electric vehicle, your digital engagement starts with a critical first step: identity verification. This process, often managed by trusted entities like Cloudflare, seems simple—a text prompt on a screen—but behind it lies a robust system built to weed out automated threats and protect sensitive data.
Understanding the Puzzle of Digital Verification
When a website prompts you to verify that you are human, what you are encountering is a carefully designed barrier against nefarious bots and cyclic hacking attempts. This is not just a temporary inconvenience but an essential part of ensuring that your business transactions, marketing strategies, and even industrial communications remain secure. The steps involved, such as checking your connection or running complex algorithms in the background, may seem like nerve-racking twists and turns, but each step is critical in building a safe digital environment.
For business owners, particularly those in industries such as automotive and electric vehicles, the assurance of this secure pathway means that every transaction is shielded from potential online threats. This process helps in protecting revenue, safeguarding confidential information, and upholding the trust of customers. In a digital ecosystem that is as dynamic as it is unpredictable, ensuring the verification process functions flawlessly is super important.
A Closer Look at Cloud-Based Security Solutions
Cloudflare’s involvement in the authentication process is one of the many aspects that illustrates how modern digital security systems work behind the scenes. The system that leads with a simple Ray ID and a verification message is a continuity of advanced cloud security protocols. These measures are strategically designed to keep websites secure and to minimize the potential of harmful attacks that could jeopardize operations ranging from small business transactions to large-scale industrial manufacturing projects.
Key reasons why these systems are so critical include:
- Protection against automated cyber attacks
- Preservation of user privacy and sensitive data
- Maintaining the integrity of data during peak traffic times
- Assuring continuity and trust in the business’s digital operations
The technology behind these verification methods may appear to be only a minute detail, but when you look at the big picture, it is super important. From promoting business confidence to preventing large-scale security breaches, secure authentication is a small twist that has big implications.
The Impact of Digital Security on Industrial Manufacturing
Industrial manufacturing has increasingly embraced digital solutions over the past decade. From automated factories to digital logistics management, the transformation has been breathtaking—and not without its own set of tricky parts. Digital security measures, including the verification processes used on websites, are integral to ensuring that the digital transformation of manufacturing remains on track and secure.
Safeguarding Production and Intellectual Property
For companies specializing in industrial components or manufacturing heavy machinery, protecting intellectual property and production processes is super important. Cyber-attacks that target manufacturing systems could lead to production downtime, data breaches, and significant financial losses. Digital security systems authenticate users and verify connections, acting as gatekeepers that ensure only authorized personnel get access to sensitive technology and information.
The following are a few ways in which digital security is woven into the fabric of industrial manufacturing:
- Securing Communication Channels: Reliable encryption methods prevent unauthorized access that might compromise production details or proprietary technology.
- Monitoring Network Activity: Advanced algorithms constantly check for suspicious movements within the network, preventing potential internal sabotage or external hacking.
- Integration with IoT Systems: In an increasingly connected environment, the Internet of Things (IoT) presents both opportunities and challenges, requiring robust security to safeguard each connected device.
For manufacturers, ensuring that every digital transaction or remote logging of data is safely verified translates into a smoother operation. It means having the tools to figure a path through complicated pieces of a highly interconnected system that depends on real-time data verification and user authentication.
Table: Digital Security Challenges in Industrial Manufacturing
| Security Challenge | Description | Potential Impact |
|---|---|---|
| Unauthorized Access | Intruders gaining access to critical production systems. | Production downtime and loss of proprietary data. |
| Data Breaches | Leak of sensitive operational or customer data. | Financial loss and damage to reputation. |
| IoT Vulnerabilities | Weak security on interconnected devices. | Potential for coordinated attacks disrupting entire networks. |
| Cyber Espionage | Theft of research and development information. | Competitive disadvantage and compromised innovation. |
This table shows a snapshot of why secure digital practices are super important for keeping industrial manufacturing running smoothly in an always-connected world.
Securing the Digital Frontier for Automotive and Electric Vehicle Sectors
As the automotive and electric vehicle (EV) industries have advanced, so too have the digital complexities associated with hardware, software, and the integration of smart systems. In an era where vehicles are evolving beyond mechanical devices into sophisticated networks of sensors and computers, digital security measures—such as secure verification protocols—play a pivotal role in maintaining system integrity.
Digital Verification: A Safety Net for Connected Vehicles
The onboard systems of modern vehicles, especially electric models, are heavily reliant on software for functions that range from navigation to energy management. Any compromise in the network security can lead to a situation where the systems are left vulnerable. The verification process, the kind you encounter when visiting a secured website, is analogous to the safety checks that vehicles now undergo remotely.
Automakers need to consider security as a core component of their product offering. This means implementing measures that not only prevent unauthorized access into the vehicle’s operating system, but also protect connected services such as remote diagnostics and over-the-air updates. The process is full of problems for car manufacturers, as they must deal with potential threats not just in the physical realm but across virtual interfaces as well.
Ensuring Consumer Safety in a High-Tech Transport Landscape
Consumers rely on the safety of their vehicles, and by extension, on the security of the digital systems that power the latest automotive and electric vehicles. Vehicle connectivity and online services are rapidly becoming a critical part of the driving experience. The verification steps that help secure online transactions are increasingly similar to those used to secure vehicle networks against malware and hacking attempts.
Car manufacturers and tech companies are now working together to craft robust systems that verify authorized access and maintain vehicle safety. Key aspects of this include:
- Implementing real-time security updates to counter emerging threats.
- Establishing secure communication channels for vehicle-to-cloud data transfer.
- Ensuring that all software updates come through verified and trusted sources.
These steps are not only super important for the safety and reliability of vehicles but also are essential for building consumer confidence in high-tech transport solutions.
How Small Businesses Are Adapting to a Secure Digital Landscape
Small businesses often find themselves at the intersection of innovation and vulnerability. While larger corporations might have vast resources to manage all aspects of digital security, smaller entities must make every dollar count and every action count double. They face unique challenges when it comes to establishing secure, user-friendly websites that still project a professional image to clients and partners.
Overcoming Intimidating Online Security Measures
For many small business owners, the idea of riding through a world of digital security protocols can be off-putting. The simple, if slightly nerve-racking, experience of verifying that you are human on a website might feel like one more barrier in an already challenging environment.
However, these measures cannot be ignored. They serve as the first line of defense in preventing attack vectors that could strip away sensitive business information or lead to financial loss. By working with accessible and affordable security solutions, small business owners can ensure that their online presence remains robust. Moreover, by delegating parts of the setup to experienced service providers, they can figure a path on how to integrate secure practices without overwhelming their everyday operations.
Strategies for Integrating Seamless Security
Adopting the right balance of security measures involves understanding customer expectations and the fine shades of online interactions. Here are some strategies small businesses can consider to ensure their sites remain both secure and user-friendly:
- Utilize Managed Security Services: Partnering with firms that specialize in cloud security can help smooth out the process of integrating verification protocols without the need for extensive in-house expertise.
- Simplify the User Experience: Even when implementing secure measures, designing a straightforward and intuitive verification flow ensures that regular users are not discouraged by what might seem like intimidating security.
- Regular System Audits: Periodic reviews of website security measures help small businesses stay on top of potential vulnerabilities and new threats, allowing for timely updates.
- Training and Awareness: Ensuring that staff understand the reasons behind security procedures can smooth the adaptation process and promote better overall cyber hygiene.
By implementing these strategies, small businesses can overcome the tangled issues and off-putting aspects of digital security, turning what might be an overwhelming obligation into a manageable and integral part of their strategy in the modern digital market.
The Intersection of Business Tax Laws and Digital Security
One of the less obvious dimensions of digital security is its interplay with business tax laws and regulatory compliance. As governments grapple with the challenges of a global digital economy, businesses must ensure that their online operations are compliant with evolving tax laws that are often full of problems and small distinctions.
Compliance in the Digital Age
Tax authorities are increasingly interested in how online transactions are conducted, especially in sectors like industrial manufacturing, automotive, and small business services. Digital verification systems can play a role in ensuring that all transactions are tracked and properly documented. This, in turn, helps businesses avoid penalties that can arise from non-compliance.
Given the small twists in tax regulation details, companies face a nerve-racking environment if they do not maintain strict digital records. The ability to trace every transaction back to a verified and authenticated source simplifies the auditing process, makes tax filing easier, and can even help in identifying any potential breaches or fraud attempts.
Creating a Secure and Compliant Digital Strategy
Businesses, regardless of size or industry, must now work through a maze of digital security protocols and tax regulations simultaneously. Here are some super important points that can aid in creating a cohesive strategy:
- Integrated Record-Keeping Systems: By aligning digital verification logs with financial documentation, companies can build a robust audit trail that meets regulatory requirements.
- Investing in Secure Payment Gateways: Payment processes that include multi-layered security checks are vital, as they ensure that not only are the transactions safe, but all details are recorded for tax purposes.
- Consulting Tax and Cybersecurity Professionals: The subtle parts of tax law requirements and digital security measures are best navigated with professional guidance to avoid pitfalls.
Ultimately, companies that manage to align these domains not only reduce their legal risks but also enhance their market credibility. The extra steps taken in ensuring secure and compliant operations can be a key differentiator in industries where trust is everything.
Economic News and the Ripple Effects of Digital Security
Economic trends have always been impacted by the evolution of technology. In recent years, the infusion of online security measures into every facet of business operations has become a driving factor for market stability and growth. Whether it’s a small business or a large industrial operation, the protection of digital infrastructure is now seen as a cornerstone of economic resilience.
Economic Stability Through Robust Cybersecurity
When businesses can concentrate on their core functions—be it manufacturing, automotive innovation, or marketing—without the persistent worry of cyber threats, this stability translates into broader economic growth. Digital security reduces the risk of catastrophic breaches that can cause economic shocks, and by extension, a secure digital ecosystem helps in fostering consumer confidence and investor interest.
There is a direct connection between the strength of a company’s online security measures and its ability to operate smoothly in a global market. As economic news often highlights rapid changes in market conditions, businesses that have built robust security systems are better prepared to weather disruption. This benefits the economy as a whole by maintaining steady growth and preventing volatility that might arise from digital fraud or data theft.
Key Economic Benefits of Secure Online Operations
The following list outlines the economic advantages that are on edge with strong digital security protocols:
- Enhanced Investor Confidence: When a company’s digital systems are secure, market analysts and investors are more likely to view it as a low-risk, adaptable organization.
- Stable Market Operations: Reliable security measures prevent the kind of large-scale disruptions that can ripple through supply chains, affecting global markets.
- Consumer Trust Boost: A secure online presence is essential for building consumer confidence, leading to higher sales and improved brand loyalty.
- Efficient Regulatory Compliance: When security protocols are aligned with legal requirements, businesses face fewer interruptions during audits, which can lead to more efficient operations and economic stability.
Viewed from an economic angle, digital security is a must-have investment. Not only does it protect individual businesses, but it also helps to drive systemic stability across industries and markets, forming the bedrock of a thriving digital economy.
Marketing in the Age of Digital Verification
Marketing strategies have evolved alongside the rise of digital security, and companies must now rework their approaches to ensure that their messaging does not clash with the technical measures that protect their online presence. In a world full of confusing bits and twisted issues, the process of verifying users becomes a part of the customer journey that can influence brand perception and trust.
Leveraging Security as a Marketing Advantage
One of the interesting angles in today’s interconnected world is using digital security to market trustworthiness. When customers see that a business takes its online protection seriously, it sends a message of reliability and professionalism. This is particularly relevant for industrial manufacturing, automotive, and small business sectors where customer data and operations are frequently targeted by malicious actors.
Marketing teams can incorporate this message into their branding, highlighting that the company is at the forefront of technology and security. By doing so, they can transform a process that might seem off-putting—like re-verifying your human status—into a positive aspect of the brand identity.
Steps to Communicate Security Confidence to Customers
Here are several strategies that marketing departments can adopt to ensure their customers understand the super important measures taken to protect their data:
- Transparent Communication: Use blog posts, newsletters, and social media updates to explain how and why security verifications are implemented. This helps demystify the process for consumers.
- Visual Proof of Security: Display badges or certifications from trusted security partners like Cloudflare on your website to visibly communicate your commitment to safety.
- Customer Education: Host webinars or include FAQs that cover the little details of online security protocols, answering common concerns and reinforcing trust.
- Feedback and Improvement: Regularly seek customer feedback regarding the verification process and adapt the user experience to ensure it remains smooth and reassuring.
This approach not only enhances customer trust but has the added benefit of differentiating the brand in competitive markets. In industries where digital interactions serve as a significant touchpoint—from small businesses to large automotive firms—a secure digital environment becomes a key selling point.
Pocketing the Benefits: Why Secure Online Practices Are a Must Across Industries
When we bring together the worlds of industrial manufacturing, automotive innovation, small businesses, and even the broader scope of economic news, one common thread runs through them all: the need for secure digital environments. Whether it’s verifying users via a Cloudflare interface or ensuring that every digital transaction is safe and recorded, the protective steps taken online have wide-reaching benefits.
Streamlined Operations and Enhanced Efficiency
At its core, a secure digital backbone enables businesses to do what they do best—innovate, produce, and market their products without constant worry about cyber threats. The simple yet secure verification process may add a slight delay for users, but it is a small price to pay for the assurance it provides.
Many businesses have come to realize that investing in secure online practices significantly boosts efficiency over time. For example, industrial manufacturing companies can operate smoother with fewer downtimes, while small businesses experience fewer interruptions during peak transaction periods. The economic benefits are evident, as fewer security breaches mean minimal financial losses and steadier consumer confidence.
Table: Industries and Their Key Digital Security Priorities
| Industry | Primary Security Concern | Key Benefit of Robust Security |
|---|---|---|
| Small Business | User authentication and data protection | Enhanced consumer trust and steady growth |
| Industrial Manufacturing | Protection of intellectual property and production systems | Operational continuity and protection against supply chain disruptions |
| Automotive/EV Sector | Securing onboard systems and connected services | Safe and reliable vehicle operations with trusted remote updates |
| Marketing Agencies | Ensuring secure customer interactions and data privacy | Improved brand credibility and customer satisfaction |
This table encapsulates how diverse industries prioritize different aspects of digital security, yet all reap significant benefits from robust and trusted online protection.
Looking Ahead: Future Trends in Digital Security and Business Practices
The intersection of technology and business is constantly evolving, and digital security is at the heart of this evolution. Recent developments suggest that verification methods and online safeguards will continue to become more sophisticated, adapting to emerging threats while balancing user convenience. Whether it’s reinforcing backend systems in industrial manufacturing or creating frictionless digital interactions for small businesses and automotive sectors, the journey ahead seems both exciting and full of unforeseeable challenges.
Anticipating the Next Generation of Security Measures
The new generation of security systems will be characterized by even tighter integration between physical operations and digital monitoring. For instance, advancements in artificial intelligence and machine learning are expected to bolster verification processes by predicting potential breaches and automatically adapting security measures in real time. Such proactive systems will help companies work through the tangled issues of cybersecurity without needing constant human oversight.
Moreover, as regulatory frameworks evolve to catch up with technological advances, businesses will need to stay agile to figure a path through a more complicated regulatory environment. Keeping pace with these changes will require significant collaboration between tech providers, government bodies, and industry experts alike.
Emerging Trends Shaping the Digital Business Landscape
Several trends are likely to shape how businesses approach online security and identity verification in the coming years:
- Biometric Verification: The adoption of fingerprint, facial recognition, and voice identification technologies are set to add an extra super important layer of security.
- Decentralized Security Platforms: Leveraging blockchain technology to create immutable records of transactions and authentications can revolutionize data security in vast networks.
- Increased Regulatory Supervision: With governments tightening digital laws, companies will be forced to adopt more integrated compliance systems that align with both security and tax requirements.
- Automated Threat Mitigation: AI-driven algorithms will help detect subtle details of potential breaches, responding quickly to incidents before they escalate into full-blown security crises.
Each of these emerging trends offers both challenges and opportunities. Companies that embrace the evolution of digital security not only enhance their operational efficiency but also set themselves apart as innovators and trusted leaders in their respective fields.
Conclusion: The Imperative of Secure Digital Transformation
In wrapping up this exploration of digital security across various business sectors, it is clear that the simple act of verifying a user’s identity—like the process observed on railtech.com—illustrates a much larger narrative. The verification process is a small yet super important piece of an intricate network that supports electric vehicles, industrial manufacturing, small businesses, and even the nuanced realm of business tax and economic sustainability.
From ensuring that vehicles operate flawlessly to allowing small businesses to confidently serve their customers, these security measures forge a path through complicated pieces of technology and ever-changing regulations. They enable companies to not only protect their sensitive data but also to steer through the twists and turns of a challenging digital landscape.
As we look into the future, the integration of advanced digital security will continue to be a key differentiator in business success and market trust. Whether you are managing a manufacturing plant, driving a futuristic vehicle, or operating a modest startup, the principles of robust verification and comprehensive cybersecurity remain central to thriving in a fast-evolving economic environment.
Ultimately, investing in secure digital practices is not just another expense—it is a strategic enabler that unlocks potential across multiple business dimensions. As technology continues to expand its reach, those who learn to work through these many challenges will undoubtedly find themselves ahead of the curve in an increasingly interconnected and competitive digital world.
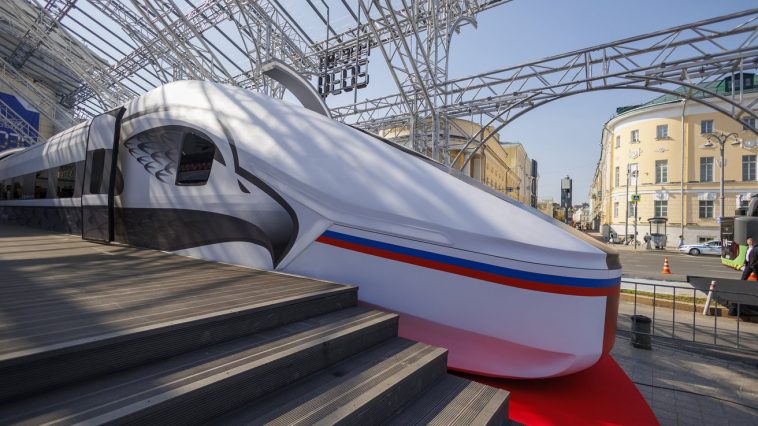
Originally Post From https://www.railtech.com/all/2025/09/26/russia-begins-building-trains-for-new-hsr-we-dont-want-to-involve-china-says-expert/
Read more about this topic at
Cloudflare test – SSL / TLS
Website security checklist | How to secure your site